The WannaCry or WannaDecryptor virus was a world-wide phenomenon, but the NHS was badly hit. Dr Saif Abed, a Founding Partner of the health IT consultancy AbedGraham that has a partnership with Highland Marketing, says a forensic inquiry should be held into what went wrong.
Otherwise, he tells Lyn Whitfield, the NHS will fail to address the fundamental issues that WannaCry exposed; and continue to ignore a significant source of clinical and patient risk.
Dr Saif Abed was driving when the first news of what was being called the #nhscyberattack came through. “I was using my phone as a sat nav, when suddenly it lit up with Twitter notifications,” he says.
“Initially, it was individuals saying: ‘I can’t get into my computer system’ and then it was news organisations saying: ‘It looks like there’s a large-scale attack underway’.”
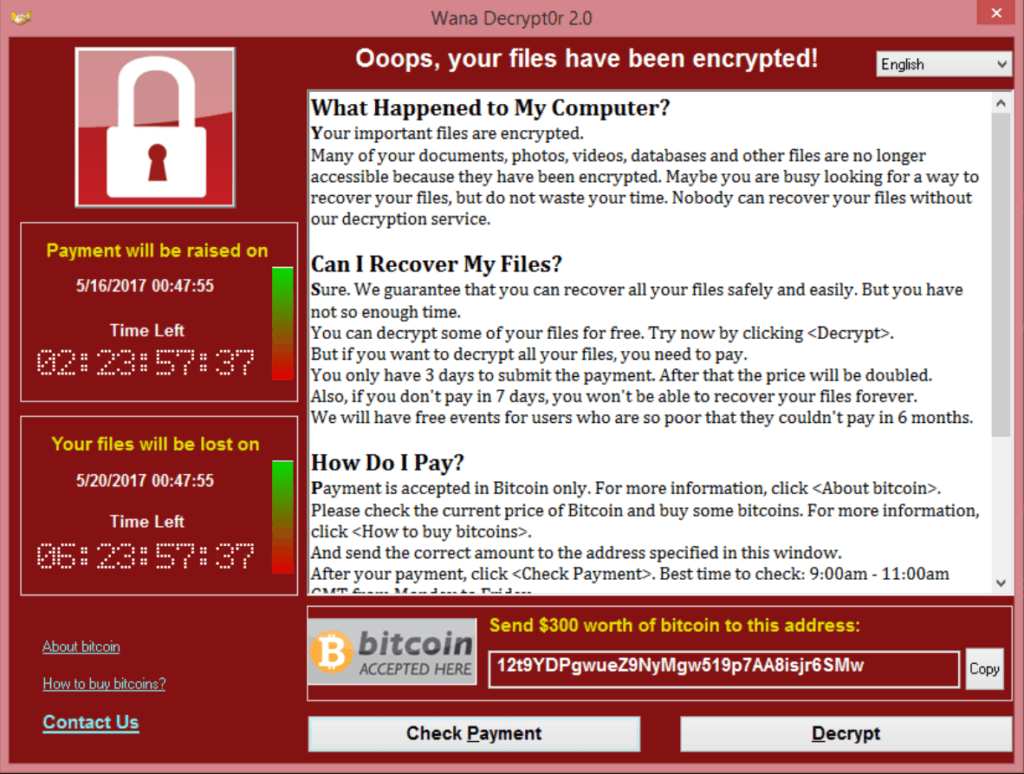
By late afternoon, it was clear that at least 16 trusts and an unknown number of GP practices had been affected by the ransomware attack. Staff trying to log into their computers were greeted by a large, red screen saying their files had been encrypted and they would need to pay a ransom in the electronic money Bitcoin to get them back.
WannaCry: one of the world’s biggest cyber attacks
However, it was also becoming clear that the NHS was not being targeted; it was being affected by the release of a virus called WannaCry or WannaDecryptor (or variations of these names) that had already impacted a telco and banks in Spain.
Dr Abed trained in medicine but has specialised in IT strategy and security, founding the AbedGraham health IT and risk consultancy that has a partnership with Highland Marketing.
As such, he was not surprised that the NHS was caught up in something bigger. “Ransomware tends to be widespread and opportunistic,” he says. “If you really wanted to launch a sustained attack against a particular organisation, then you would use something more specialist and directly malicious than this.”
Maps tracking the spread of the malware on Friday afternoon showed it moving fast across Asia, southern Europe and Russia. It was brought to a sudden halt in the early hours of Saturday morning when a cybersecurity researcher, @malwaretechblog, registered a domain name buried deep in the code and found that it acted as a ‘kill switch’.
Even so, the NHS was hit hard. Some trusts, and boards in Scotland had to close their A&E departments or urge patients to attend only if they had life threatening conditions, as delays built up. There were numerous reports of appointments being cancelled and transfers and discharges delayed.
For the NHS, a simple XPlanation misses the point
The basic advice to see off ransomware is always to have good perimeter security to stop viruses getting through, to train staff not to click on suspect links, and to have good backup so systems can be restored without paying the ransom.
Perhaps inevitably, news organisations and social media commentators looking to understand why the NHS had been so badly affected by WannaCry focused on the first, technology layer.
Surveys, including the digital maturity assessment of trusts that NHS England conducted last year, have shown that a majority of trusts are still running computers running Windows XP.
This is a Microsoft operating system that has not been supported since 2014 (or, for the UK public sector, 2015) and is no longer ‘patched’ against the sort of known vulnerability that WannaCry exploited.
As the weekend’s general election campaign interviews kicked into gear, there were accusations that the outgoing government had allowed a deal with Microsoft to support XP to lapse, and that the NHS was too starved of funds to move onto more modern software.
A national enquiry is needed
However, Dr Abed argues this misses the point. He says that WannaCry has exposed a bigger lack of investment in the NHS; in board level engagement in IT issues, in IT leadership, in basic infrastructure, and in staff training.
He also argues that a full investigation is needed to find out exactly what role each of these played. “We need a forensic investigation into this, in part to avoid inappropriately blaming specific bits of software, or people,” he says.
“I have seen a lot of tweets apportioning blame: ‘It’s all the fault of the IT department’ or ‘how could people be so irresponsible as to click on a link’; but it’s not that straightforward.
“We have to ask why this software is still out there, why it is unpatched, why there hasn’t been the investment in clinical leadership to make people aware of the dangers, why there weren’t the people and processes in place to respond when it happened.
“Also, if we see this as only a technology issue, we run the risk of not seeing the situation for what it really is; a clinical risk and patient safety issue.”
This is not a tech issue, it’s a clinical and patient safety issue
Two days after WannaCry hit, on Sunday afternoon, NHS Digital issued a statement explaining that it was “continuing to work around the clock” to support NHS organisations hit by the attack; suggesting that it was going to take some trusts some time to recover.
It’s too early to say why some trusts and boards were hit by WannaCry, when others dodged it, or why some have recovered so much more easily from back-up than others.
However, Dr Abed says the disparities illustrate another, broader problem; NHS organisations have very different levels of digital maturity, yet funds for NHS IT tend to be announced for specific projects, and then delayed or clawed back before anything much is achieved on a wide scale.
“We need to invest consistently in infrastructure and people and processes,” he says. “That is why we need a forensic inquiry, and one that leads to immediate action, not one that takes two years and then issues a report.
“If we can pinpoint the problems, we can build a co-ordinated relationship between suppliers, the government and NHS organisations that addresses the problems in a way that meets clinical need.”
Not over yet?
The @malwaretechblog expert who stopped the WannaCry attack has been hailed as an “accidental hero” for his actions. However, he himself told the Guardian that it could easily start up again.
Dr Abed agrees; it is not yet clear what will happen as the world goes back to work on Monday morning. “This malware is based on a fault that was exploited by the US National Security Agency, and then leaked online,” he says.
“It was stopped by triggering a kill switch, but that could be very easy to remove in another version of the ransomware. So, we might see a new wave of attacks happening, and those attacks might not have easily identifiable kill switches in place. We could see an unstoppable attack.”
At various levels, then, the advice remains: have good perimeter security and apply all available patches, never click on a link about which you have the slightest doubt, sort out backup and have a plan for when things still go wrong.
But Dr Abed reiterates that this is not enough; the NHS needs to hold an enquiry into WannaCry and then get to grips with the fundamental problems that it exposed. “The part of me that is a clinician is hoping that this will not be siloed as a technology issue,” he says.
“This needs to be seen as a national challenge and as a board-level priority, because it is a clinical safety and a patient care issue. It just so happened that this particular point of failure was based on technology.”
Dr Saif Abed profile
Dr Saif Abed (@Saif_Abed) is, by background, an NHS doctor and currently the Founding Partner at Abed Graham AbedGraham, an exclusively clinically based European health IT strategy and risk consultancy. He studied medicine and anatomy at St George’s Hospital Medical School in London before studying management at the University of Cambridge. Additionally, he is currently undertaking a GCHQ accredited masters degree in Software and Systems Security at the University of Oxford.
Dr Abed has extensively advised large technology organisations, including Microsoft, Citrix and Imprivata, as well as healthcare providers and government agencies in areas including clinical workflows, policy analysis and information governance & risk management. He is trained by NHS Digital as a Clinical Safety Officer for health IT.



